How to Secure PHP – PHP is a great scripting language with a lot of capabilities. PHP is often used on web pages in conjunction with HTML. Once a server receives a request, it hands it off to the PHP handler.
The PHP handler will process the HTML and PHP code and output the new HTML. This creates a web page that was altered on the server before being transferred to the original requestor.
This ability makes PHP powerful, but it also makes it a potential security risk. Since this language modifies pages in between when a local machine makes a request and when the server returns that page to the local device, it creates a point where hackers can modify data.
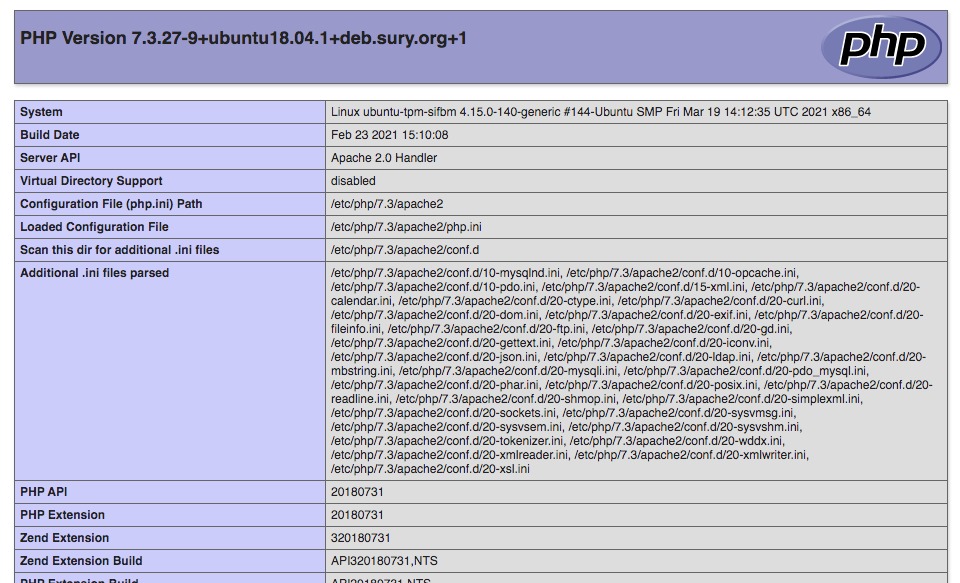
In this article, we’re going to discuss some of PHP’s settings and go over some ways to increase the security of PHP and your server. By modifying the PHP.ini file, you can change what PHP scripts are permitted to do.
How to Secure PHP ? PHP.ini Configuration Settings
-
allow_url_fopen
allow_url_fopen = Off
This setting allows or disallows PHP from using URLs from being used in statements such as include(). While there are advantages to this behavior, it opens up your server to the possibility of Remote File Inclusion (RFI) attacks.
In an RFI attack, the attacker includes a URL in an HTTP query with the goal of tricking your script into running their include versus yours.
Note that setting allow_url_fopen to off prevents you from pulling content from either sites. If this is functionality you need for your site, you’ll need to look into other methods of preventing RFI attacks such as verifying the URLs in your script, before running them.
-
Setup Error Logging
DISPLAY_ERRORS =Off display_startup_errors = Off log_errors = On error_reporting = E_ALL Fastcgi.logging = 0
These settings prevent PHP from displaying errors on the web pages running your scripts. Displaying the error messages from PHP can give attackers valuable clues on how to penetrate your server’s security.
If you need to review error messages, you can look in the PHP error log. To find the location of the PHP error log, check the error_log variable in the ini file.
error_log = /home/yourUserID/public_html/phperr.txt
You system will append to this file indefinitely. Make sure the file isn’t publicly accessible and that you check and clear it out regularly.
-
Disable register_globals
register_globals = Off
If the ini setting register_globals is on variables passed to your scripts from URLs will automatically be passed into your script. You should disable this setting to make it harder for attackers to inject code into your site.
-
Limit Memory Usage and Script Execution Times
memory_limit=16M upload_max_filesize=2M post_max_size=8M max_input_nesting_levels=64 max_execution_time=30 max_input_time=60
These ini settings will set limits to both the memory usage and execution times of your script. By doing this an attacker can’t attempt to exploit time out or low memory states to exploit your system.
-
Set the open_basedir
open_basedir="c:inetpub"
Setting this in the PHP ini file limits where PHP can read and write files. This prevents attackers from using PHP to do things like overwrite configuration files.
-
Set expose_php
expose_php = Off
Setting this will conceal that the server is running PHP.
Knowing to set these basic settings in the PHP ini file will help you secure the PHP scripts running on your web server. With just a few minutes you can take a few steps to reduce the likelihood your website will be taken over.
Whenever you setup a new web server, make sure to take steps to secure it so you don’t lose valuable data.