Patching OpenSSL for the Heartbleed Vulnerability
A security vulnerability in OpenSSL dubbed Heartbleed has been found. This vulnerability was only recently discovered openly, but has been “in the wild” for over a year. It’s important to update your local version of OpenSSL to correct this issue. This brief guide will walk you through ensuring that the patch is installed on your Linode, and suggest additional steps you can take to ensure your server’s security. As always, we suggest having backups of your system prior to making any changes.
This guide is written for a non-root user. Commands that require elevated privileges are prefixed with sudo. If you’re not familiar with the sudo command, you can check our Users and Groups guide.
Installing the Patched Version
Here are the steps for ensuring you have the patched versions of OpenSSL on our most popular distros. If you’ve compiled from source, you’ll want to compile and reinstall using version 1.0.1g. Alternately you can recompile previous versions with the OPENSSL_NO_HEARTBEATS flag enabled to close the vulnerability.
Ubuntu and Debian
-
Check to see what your current OpenSSL version is:
$ openssl version -a OpenSSL 1.0.1e 11 Feb 2013 built on: Sat Feb 1 22:14:33 UTC 2014 platform: debian-amd64 options: bn(64,64) rc4(16x,int) des(idx,cisc,16,int) blowfish(idx) compiler: gcc -fPIC -DOPENSSL_PIC -DZLIB -DOPENSSL_THREADS -D_REENTRANT -DDSO_DLFCN -DHAVE_DLFCN_H -m64 -DL_ENDIAN -DTERMIO -g -O2 -fstack-protector --param=ssp-buffer-size=4 -Wformat -Werror=format-security -D_FORTIFY_SOURCE=2 -Wl,-z,relro -Wa,--noexecstack -Wall -DMD32_REG_T=int -DOPENSSL_IA32_SSE2 -DOPENSSL_BN_ASM_MONT -DOPENSSL_BN_ASM_MONT5 -DOPENSSL_BN_ASM_GF2m -DSHA1_ASM -DSHA256_ASM -DSHA512_ASM -DMD5_ASM -DAES_ASM -DVPAES_ASM -DBSAES_ASM -DWHIRLPOOL_ASM -DGHASH_ASM OPENSSLDIR: "/usr/lib/ssl"Pay attention to the
built on:line. Versions built before April 7th are vulnerable. -
For Debian and Ubuntu systems, run these commands to update and upgrade your packages:
sudo apt-get update sudo apt-get upgrade -
During the upgrade, you may be given a prompt like the one below. This window warns you about the security issue, and lists services that utilize OpenSSL and need to be restarted to apply the patch. You can add any additional services, by matching the init.d script name in this field.
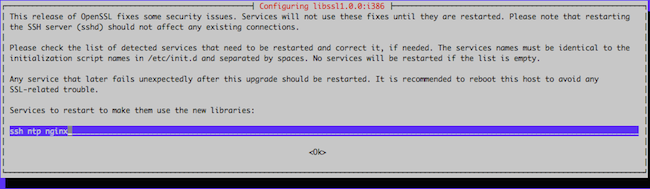
If you do not receive this prompt, be sure to manually restart any services that use OpenSSL.
-
After updating, run
openssl version -aagain to confirm the newer build:openssl version -a OpenSSL 1.0.1 14 Mar 2012 built on: Mon Apr 7 20:33:29 UTC 2014 ...
CentOS
-
Check to see what your current OpenSSL version is:
openssl version -a OpenSSL 1.0.1e-fips 11 Feb 2013 built on: Wed Jan 8 18:40:59 UTC 2014 platform: linux-x86_64 options: bn(64,64) md2(int) rc4(16x,int) des(idx,cisc,16,int) idea(int) blowfish(idx) compiler: gcc -fPIC -DOPENSSL_PIC -DZLIB -DOPENSSL_THREADS -D_REENTRANT -DDSO_DLFCN -DHAVE_DLFCN_H -DKRB5_MIT -m64 -DL_ENDIAN -DTERMIO -Wall -O2 -g -pipe -Wall -Wp,-D_FORTIFY_SOURCE=2 -fexceptions -fstack-protector --param=ssp-buffer-size=4 -m64 -mtune=generic -Wa,--noexecstack -DPURIFY -DOPENSSL_IA32_SSE2 -DOPENSSL_BN_ASM_MONT -DOPENSSL_BN_ASM_MONT5 -DOPENSSL_BN_ASM_GF2m -DSHA1_ASM -DSHA256_ASM -DSHA512_ASM -DMD5_ASM -DAES_ASM -DVPAES_ASM -DBSAES_ASM -DWHIRLPOOL_ASM -DGHASH_ASM OPENSSLDIR: "/etc/pki/tls" engines: dynamicPay attention to the
built on:line. Versions built before April 7th are vulnerable. -
To update OpenSSL from the repositories, run:
yum -y install opensslAfter updating, run
openssl version -aagain to confirm the newer build:openssl version -a OpenSSL 1.0.1e-fips 11 Feb 2013 built on: Tue Apr 8 02:39:29 UTC 2014 ... -
Be sure to manually restart any services that use OpenSSL.
Fedora
-
Check to see what your current OpenSSL version is:
openssl version -a OpenSSL 1.0.1e-fips 11 Feb 2013 built on: Fri Dec 20 13:57:26 UTC 2013 platform: linux-x86_64 options: bn(64,64) md2(int) rc4(16x,int) des(idx,cisc,16,int) idea(int) blowfish(idx) compiler: gcc -fPIC -DOPENSSL_PIC -DZLIB -DOPENSSL_THREADS -D_REENTRANT -DDSO_DLFCN -DHAVE_DLFCN_H -DKRB5_MIT -m64 -DL_ENDIAN -DTERMIO -Wall -O2 -g -pipe -Wall -Wp,-D_FORTIFY_SOURCE=2 -fexceptions -fstack-protector-strong --param=ssp-buffer-size=4 -grecord-gcc-switches -m64 -mtune=generic -Wa,--noexecstack -DPURIFY -DOPENSSL_IA32_SSE2 -DOPENSSL_BN_ASM_MONT -DOPENSSL_BN_ASM_MONT5 -DOPENSSL_BN_ASM_GF2m -DSHA1_ASM -DSHA256_ASM -DSHA512_ASM -DMD5_ASM -DAES_ASM -DVPAES_ASM -DBSAES_ASM -DWHIRLPOOL_ASM -DGHASH_ASM OPENSSLDIR: "/etc/pki/tls" engines: dynamicPay attention to the
built on:line. Versions built before April 7th are vulnerable. -
On Fedora systems, the patched version is currently being propagated through mirrors. You can update from the repositories with the following command:
sudo yum -y install openssl -
After updating, run
openssl version -aagain to confirm the newer build:openssl version -a OpenSSL 1.0.1e-fips 11 Feb 2013 built on: Tue Apr 8 00:32:22 UTC 2014 ... -
Be sure to manually restart any services that use OpenSSL.
Reissue Certificates
The Heartbleed security bug would allow an attacker to read a portion of the memory on an unprotected system, including private keys used in SSL key pairs. It’s suggested that you reissue all key pairs, and revoke ones made previously. This can include keys used to create SSL certificates for web and mail servers. This means new SSL certificates should be generated or purchased.
You can follow the instructions here to create a new certificate signing request (CSR) and key.
Additional Security Steps
While this security flaw has only recently been discovered openly, it has existed on many servers for well over a year. This means that any third party services you use that employ SSL encryption have been vulnerable. It’s suggested that you ensure that said services patch their systems, then reset your passwords.
More Information
You may wish to consult the following resources for additional information on this topic. While these are provided in the hope that they will be useful, please note that we cannot vouch for the accuracy or timeliness of externally hosted materials.
- Heartbleed.com
Join our Community
Find answers, ask questions, and help others.
This guide is published under a CC BY-ND 4.0 license.