Very Secure FTP daemon, or simply vsFTPd is a lightweight piece of software with great ability to customize. In this tutorial we are going to secure an already existing installation on a Debian system using our own self-signed SSL/TLS certificate. Despite it’s written for Debian it should work on most Linux distributions such as Ubuntu and CentOS for instance.
Installation of vsFTPd
On a fresh Linux VPS you need to install vsFTPd first. Although you will find the basic steps to install vsFTPd in this tutorial I recommend you to read these two more detailed tutorials as well: Setup vsFTPd on Debian/Ubuntu and Installing vsFTPd on CentOS. All steps regarding the installation are more carefully explained there.
Installation on Debian/Ubuntu:
apt-get install vsftpd
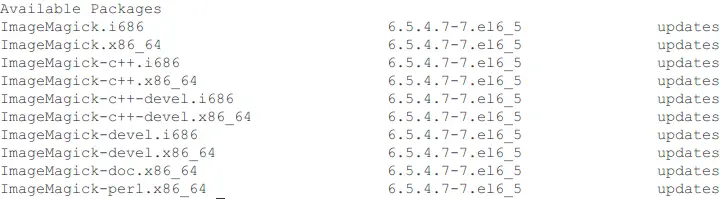
Installation on CentOS:
yum install epel-release
yum install vsftpd
Configuration
Open the configuration file: /etc/vsftpd.conf in your favorite text editor, in this tutorial we use nano.
nano /etc/vsftpd.conf
Paste the following lines into the configuration:
anonymous_enable=NO
local_enable=YES
write_enable=YES
chroot_local_user=YES
Finish up by restarting your vsFTPd daemon:
/etc/init.d/vsftpd restart
You should now be able to login as any local user over FTP, now let’s move on and secure this software.
Generate a self signed certificate
A self signed certificate is typically used in a public key agreement protocol, you will now use openssl to generate a public key and a corresponding private key. First of all we need to make a directory to store these two key files, preferably in a safe location normal users can not access.
mkdir -p /etc/vsftpd/ssl
Now to the actual generation of the certificate, we are going to store both the keys in the same file (/etc/vsftpd/ssl/vsftpd.pem):
openssl req -x509 -nodes -days 365 -newkey rsa:4096 -keyout /etc/vsftpd/ssl/vsftpd.pem -out /etc/vsftpd/ssl/vsftpd.pem
After executing the command you will be asked a few questions such as country code, state, city, organization name etc. use your own or your organizations information. Now the most important line is the Common name which must match the IP address of your VPS, alternatively a domain name pointing at it.
This certificate will be valid for 365 days (~1 year), it will use the RSA key agreement protocol with a key length of 4096 bits, and the file containing both the keys will be stored in the new directory we just created. For more details about key length and it’s relation to security see this: Encryption II recomendations.
Install the new certificate in in vsFTPd
To start using our new certificate and thus provide encryption, we need to open up the configuration file again:
nano /etc/vsftpd.conf
We need to add the paths to our new certificate and key files. Since they are stored in the same file it should be the same inside the configuration as well.
rsa_cert_file=/etc/vsftpd/ssl/vsftpd.pem
rsa_private_key_file=/etc/vsftpd/ssl/vsftpd.pem
We must add this line to make sure SSL will be enabled:
ssl_enable=YES
Optionally we may block anonymous users from using SSL, since encryption isn’t needed on a public FTP server.
allow_anon_ssl=NO
Next we need to specify when to use SSL/TLS, this will enable encryption both for data transfer and login credentials
force_local_data_ssl=YES
force_local_logins_ssl=YES
We may also specify what versions and protocols to be used. TLS is generally more secure than SSL and thus we may allow TLS and at the same time block older versions of SSL.
ssl_tlsv1=YES
ssl_sslv2=NO
ssl_sslv3=NO
Require SSL reuse and the usage of high ciphers will also help improve the security. From vsFTPd’s man pages:
require_ssl_reuse
If set to yes, all SSL data connections are required to exhibit SSL session reuse (which proves that they know the same master secret as the control
channel). Although this is a secure default, it may break many FTP clients, so you may want to disable it. For a discussion of the consequences, see
http://scarybeastsecurity.blogspot.com/2009/02/vsftpd-210-released.html (Added in v2.1.0).ssl_ciphers
This option can be used to select which SSL ciphers vsftpd will allow for encrypted SSL connections. See the ciphers man page for further details. Note
that restricting ciphers can be a useful security precaution as it prevents malicious remote parties forcing a cipher which they have found problems with.
require_ssl_reuse=YES
ssl_ciphers=HIGH
Finish up by restart the vsftpd daemon
/etc/init.d/vsftpd restart
Confirm installation
And that’s it, you should now be able to connect to your server and confirm that everything works. If you are using FileZilla a dialog containing your organization information (or whatever you entered when generating the certificate earlier) should open upon connection. The output should then look similar to this:
Status: Connection established, waiting for welcome message...
Status: Initializing TLS...
Status: Verifying certificate...
Status: TLS connection established.
To learn more about vsFTPd, check out it’s manual pages:
man vsftpd
Want to contribute?
You could earn up to $300 by adding new articles
Suggest an update
Request an article